IT Security & Information Security - Understandable and Practical
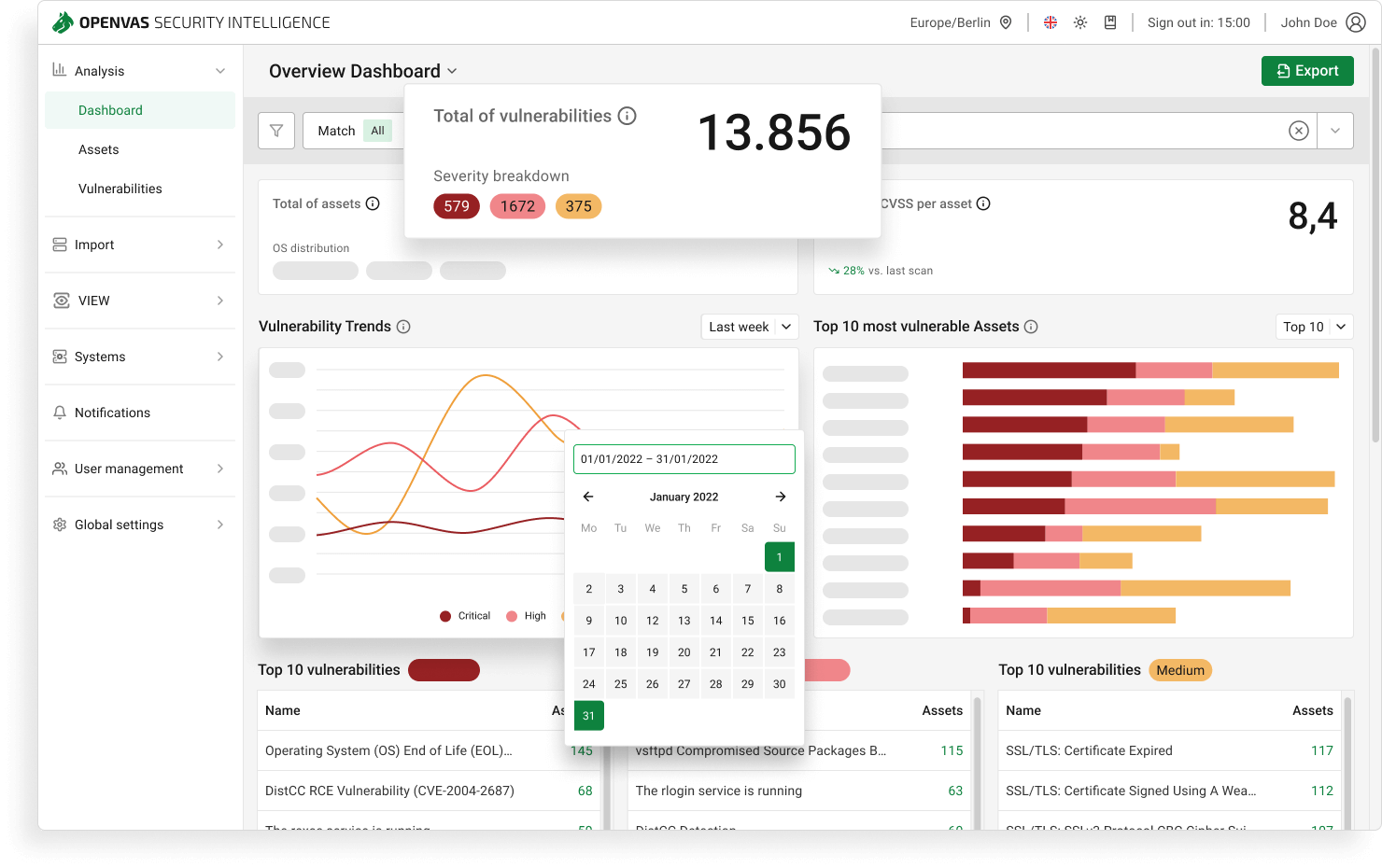
Definitions, key differences, real world examples, and a checklist for businesses and public sector organisations. Automatically identify and prioritise vulnerabilities with OPENVAS.
Get your free consultation