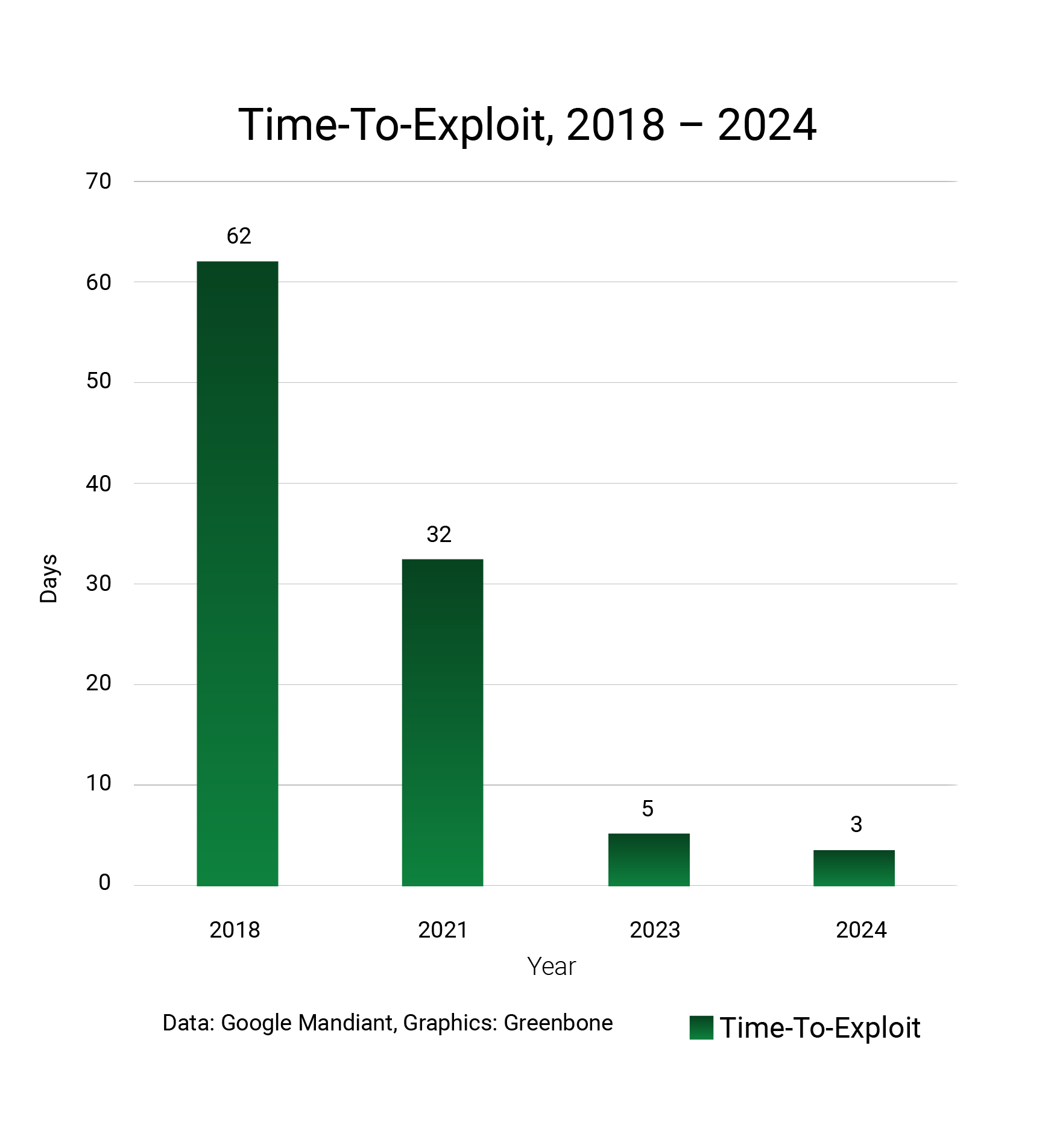
Security experts are observing a worrying trend: the time to exploit (TTE), i.e. the time between a security vulnerability becoming known and being exploited by malicious actors, has been falling dramatically in recent times.

At the same time, attackers are becoming increasingly skilled at concealing their presence in a successfully hacked network. Experts refer to the time it takes to establish a foothold and then gain unauthorized access to company resources before being detected (and removed) as “dwell time”. The shorter this time, the better for those under attack. Even the most talented hacker needs time and can cause more (permanent) damage the longer they remain undetected and unobserved.
The Enemy Is Listening – and May Already Be There
Alarmingly, dwell time is increasingly reaching months or even years, as was the case with Sony and the US Office for Personal Management. There, attackers were able to operate undisturbed for more than twelve months. As a result, more than 10 terabytes of data were stolen from the Japanese technology group.
The fear of hidden intruders is great; after all, no one can say with certainty whether a malicious listener is already on their own network. It happens. In the 2015 Bundestag hack, for example, it was not the Bundestag’s own monitoring system that informed the German authorities about strange activities by third parties (Russian APT hacker groups) on the Bundestag network, but a “friendly” intelligence service. How long and how many actors had already been active in the network at that point remained unclear. The only thing that was clear was that there was more than one, and that the friendly intelligence services had been watching for some time.
Detection, Prevention and Response Increasingly Critical
This makes it more important to ensure that attackers do not gain access to the system in the first place. But this is becoming increasingly difficult: as reported by experts at Google’s Mandiant, among others, the response time available to companies and software operators between the discovery of a vulnerability and its exploitation has fallen rapidly in recent years, from 63 days in 2018 to just over a month in recent years.
Less and Less Time to Respond
In 2023, administrators had an average of only five days to detect and close vulnerabilities. Today it is already less than three days.
But that’s not all. In the past, security vulnerabilities were often exploited after patches became available, i.e., after experienced administrators had already secured their systems and installed the latest patches. These so-called “N-day vulnerabilities” should not really be a problem, as fixes are available.
Improved Discipline with Side Effects: Attackers Learn
Unfortunately, in the past, discipline (and awareness) was not as strong in many companies, and the issue was neglected, inadvertently contributing to the spread of automated attack methods such as worms and viruses. But there is good news here too: in 2022, attacks via N-day vulnerabilities still accounted for 38% of all attacks, but by 2023 this figure will fall to just 30%.
At first glance, this sounds good because administrators can find and fix known vulnerabilities for which patches are available more quickly and effectively. After years of poor discipline and a lack of update and patch strategies, the major and successful ransomware incidents have certainly also helped to convey the scope and importance of proper vulnerability management to the majority of those responsible.
Two-thirds Are now Zero-days
But there is also a downside to these figures: more than two-thirds of all attacks are now based on zero-day vulnerabilities, i.e., security gaps for which there is no patch yet – in 2023, this figure was as high as 70%. Criminal groups and attackers have reacted, learned and professionalized, automated and greatly accelerated their activities.
Without automation and standardization of processes, without modern, well-maintained and controlled open-source software, administrators can hardly keep up with developments. Who can claim to be able to respond to a new threat within three days?
Powerless? Not with Greenbone
When attackers can respond faster to new, previously unknown vulnerabilities and have also learned to hide themselves better, there can only be one answer: the use of professional vulnerability management. Greenbone solutions allow you to test your network automatically. Reports on the success of measures give administrators a quick overview of the current security status of your company.