Since 2021-04-30, the latest GOS version – version 21.04 – is available and, as always, it brings a lot of new features and improvements! What exactly? Get an overview of all important changes with GOS 21.04 here!
Since 2021-04-30, the latest GOS version – version 21.04 – is available and, as always, it brings a lot of new features and improvements! What exactly? Get an overview of all important changes with GOS 21.04 here!
New Hardware Models for Our Midrange Class Available
A new hardware generation has been introduced for the Midrange Class hardware appliances, which are used for medium-sized companies or for branch offices of large, distributed companies.
The new hardware now uses SSD-type hard disks instead of HDD, which are 10 times faster, quieter and lighter. There is also more hard disk space available. The RAM has also been improved. It is now DDR4 instead of DDR3, which makes it significantly faster with a higher clock rate (3200 MHz). Furthermore, twice to four times as much main memory is available than before. In addition, a new, faster CPU of the latest generation has been installed. The ports of the appliances also change: instead of 6 ports GbE-Base-TX and 2 ports 1 GbE SFP, there are now 8 ports GbE-Base-TX and 2 ports 10 GbE SFP+.
The model names remain unchanged.
Boreas Alive Scanner now as Standard
The Boreas Alive Scanner is a host alive scanner that identifies the active hosts in a target network. It was introduced with GOS 20.08, but was previously optional. With GOS 21.04, the Boreas Alive Scanner became standard.
Compared to the Nmap port scanner, which was previously used by default, the Boreas Alive Scanner is not limited in terms of the maximum number of alive scans performed simultaneously and is therefore faster.
The Boreas Alive Scanner significantly reduces scanning time for large networks with a small percentage of reachable hosts. This also makes it possible to get the first scan results faster, regardless of the percentage of alive hosts in the network.
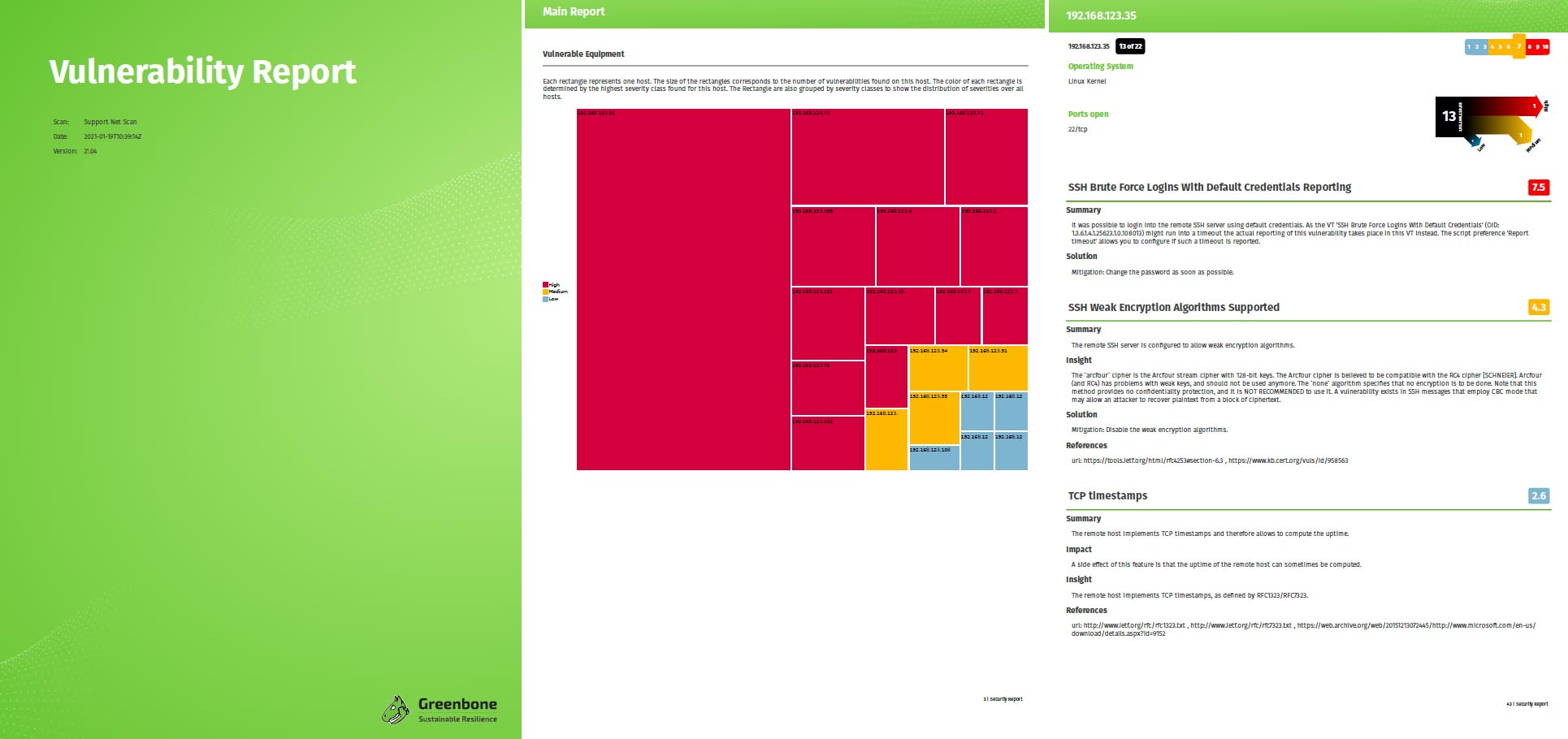
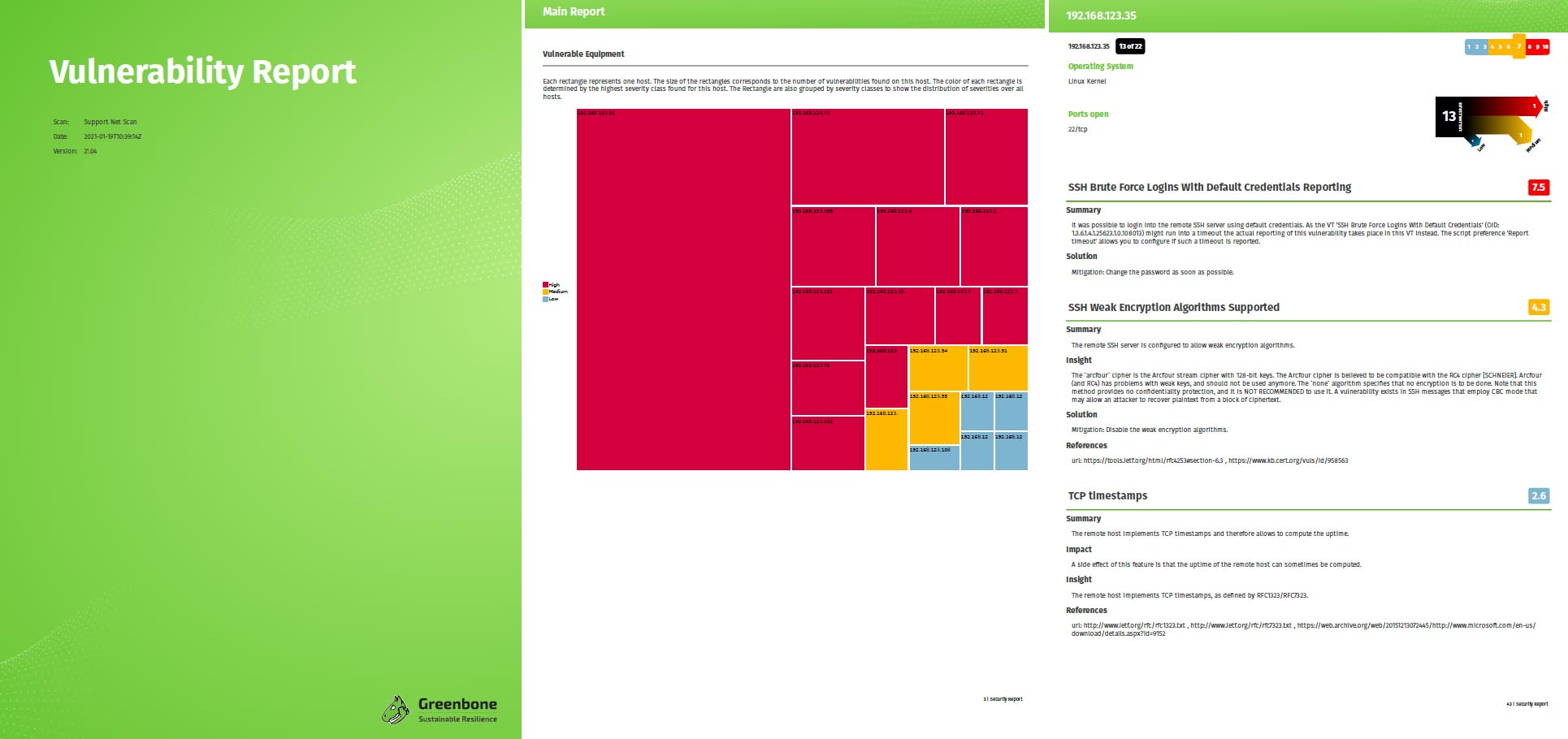
Clearer Results Thanks to New Report Formats
Two additional report formats are now available for exporting reports, replacing the previous standard report formats: Vulnerability Report PDF and Vulnerability Report HTML. The report formats are clearly structured and easy to understand. Specific information relevant to the target group can be quickly identified and understood.
The report formats provide a basis for user-defined reports, which are planned for future GOS versions.
New Network Backend for a more Stable Connection
With GOS 21.04, the network configuration backend in GOS has been improved by introducing the gnm networking mode. This prevents connection losses in certain network configurations as well as connection problems with SSH sessions. In addition, the GSM no longer needs to be restarted after certain network settings have been changed.
New Hypervisors for Our Virtual Appliances
The officially supported hypervisors for the virtual appliances have been changed with GOS 21.04. The GSM EXA/PETA/TERA/DECA and 25V can be used with Microsoft Hyper-V, VMware vSphere Hypervisor (ESXi), and Huawei FusionCompute; the GSM CENO can be used with Microsoft Hyper-V and VMware vSphere Hypervisor (ESXi); and the GSM ONE can be used with Oracle VirtualBox, VMware Workstation Pro, and VMware Workstation Player. Additionally, GOS 21.04 supports the ARM instruction set on Huawei FusionCompute.
Improvement of the Web Server, Ciphers and Web Certificates
With GOS 21.04, the nginx web server is used in addition to the Greenbone Security Assistant Daemon (gsad). This web server uses OpenSSL instead of GnuTLS to define the available ciphers and protocols of the server. There is now a new menu in the GOS administration menu for configuring the TLS version. In addition, the menu for configuring the ciphers has been adapted.
Another change can be found in the generation of HTTPS certificates. Here it is now possible to define one or more Subject Alternative Name(s) (SAN). These are used to cover multiple domain names and IP addresses with one certificate.
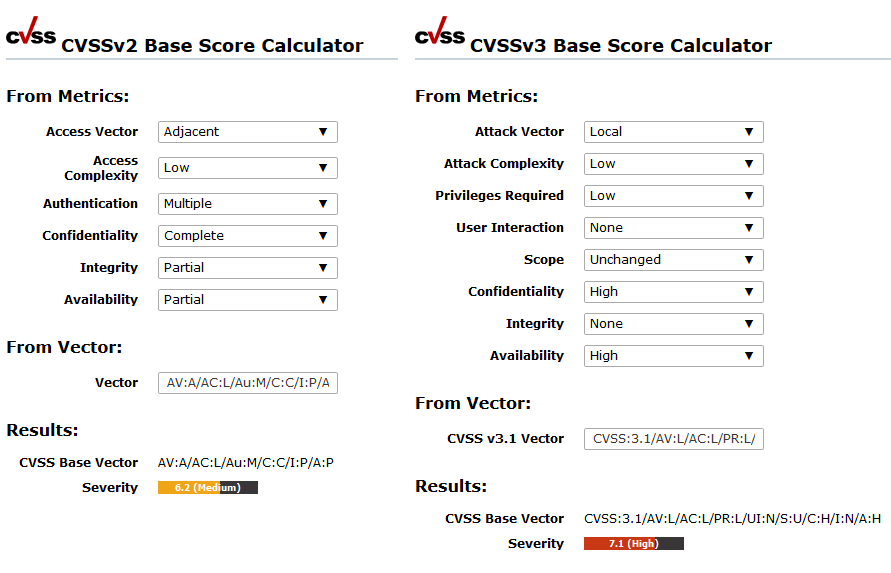
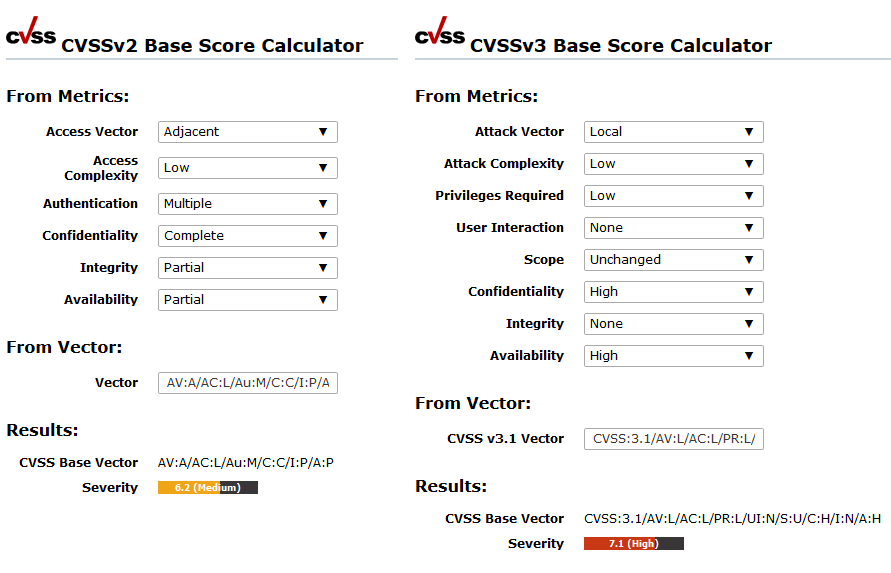
CVSS v3.0/v3.1 Support for Severity Calculation
CVSS version 3.0 and 3.1 are now supported for calculating the severity of CVEs (Common Vulnerability Enumeration).
VTs and CVEs can contain version 2 and/or version 3.0/3.1 CVSS data. If a VT/CVE contains both CVSS v2 data and CVSS v3.0/v3.1 data, the CVSS v3.0/v3.1 data is always used and displayed.
The page CVSS Calculator now contains both a calculator for CVSS v2 and a calculator for CVSS v3.0/v3.1.
Open Scanner Protocol Makes all Sensor GSMs Lightweighted
Already with GOS 20.08 it was optionally possible for all sensors to be controlled via the Open Scanner Protocol (OSP). This results in the sensors becoming lightweighted and avoids the need for additional credentials on the sensor.
With GOS 21.04, only OSP is now used as the protocol to control a sensor GSM via a master GSM. The Greenbone Management Protocol (GMP) is no longer used.
Simplified and More Intuitive Functions on the Web Interface
With GOS 21.04, some minor changes have also been made to GOS and the web interface to make GSM operation and scanning clearer and more intuitive.
For example, the Auto-FP function and the alternative severity class schemes – BSI Vulnerability Traffic Light and PCI-DSS – have been removed.
Some devices – especially IoT devices – can crash when scanned across multiple IP addresses simultaneously. This can happen, for example, if the device is connected over IPv4 and IPv6. With GOS 21.04, it is possible to avoid scanning over multiple IP addresses at the same time by using the new setting Allow simultaneous scanning via multiple IPs when creating a target.
See for Yourself!
Check out our new features and changes for yourself! New appliances with GOS 21.04 are now available and existing appliances can also be upgraded to the latest version. Also our free trial version can be used with GOS 21.04.


 Since 2021-04-30, the latest GOS version – version 21.04 – is available and, as always, it brings a lot of new features and improvements! What exactly? Get an overview of all important changes with GOS 21.04 here!
Since 2021-04-30, the latest GOS version – version 21.04 – is available and, as always, it brings a lot of new features and improvements! What exactly? Get an overview of all important changes with GOS 21.04 here!