it-sa 2024 in Nuremberg was a great success not only for the organizers but also for us: three days full of inspiring conversations, new contacts and important insights into the current security requirements of existing and potential customers. As one of the most important trade fairs for IT security in Europe, it-sa was the ideal platform for us to present the latest developments to a broad audience. Our keynote, held by CEO Dr. Jan-Oliver Wagner, attracted numerous trade visitors. Under the title “Be secure and stay secure”, he provided insights into the importance of our portfolio for proactive corporate security.

The Greenbone team at it-sa 2024 was pleased to welcome twice as many visitors as in the previous year.
Keynote: Vulnerability Management as the Basis for Cyber Security
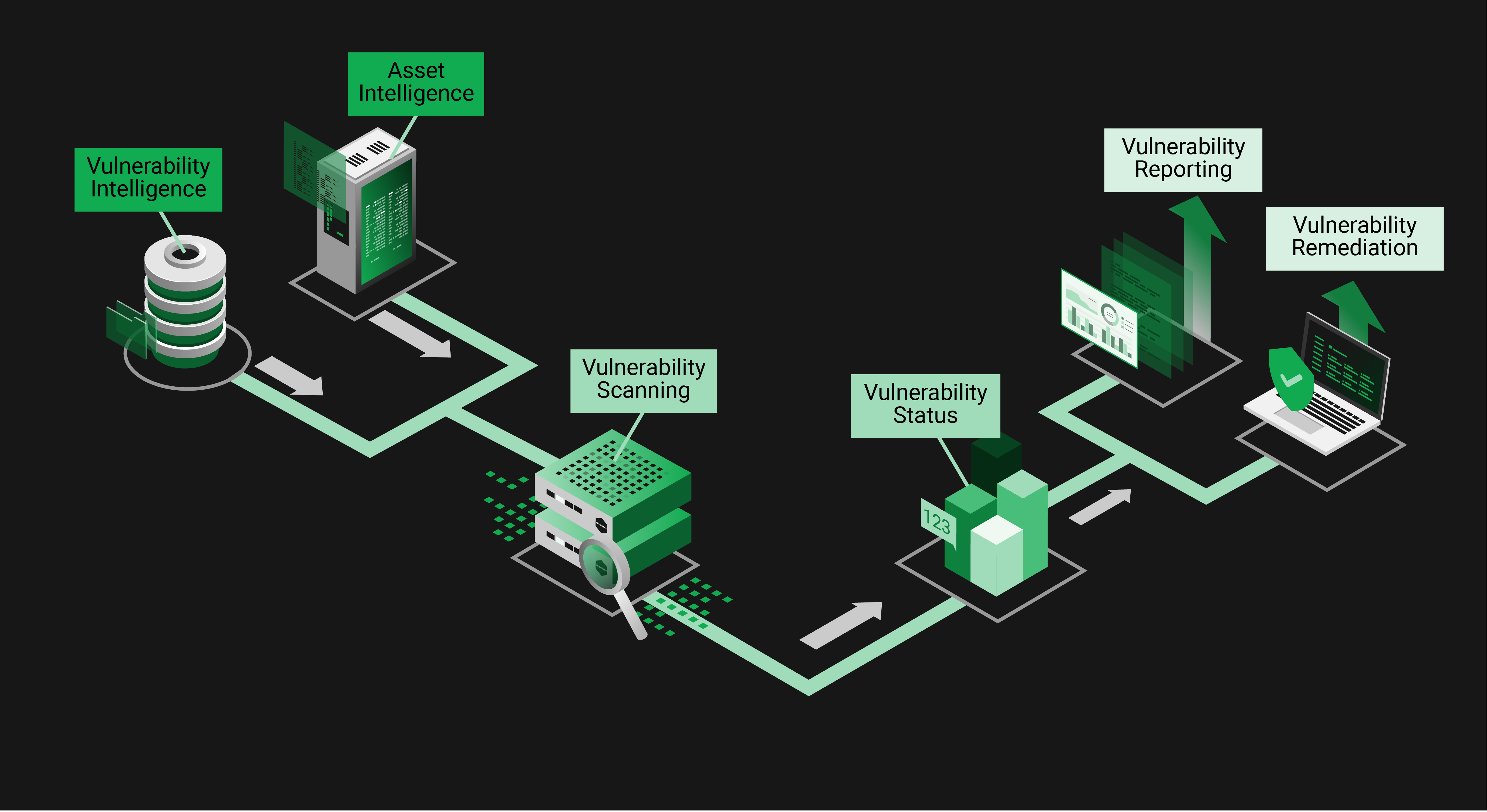
In his keynote, Jan-Oliver Wagner spoke about the growing importance of vulnerability management as the fundamental building block of a comprehensive security strategy. Companies and organizations of all sizes are facing the challenge of dealing with the ever-increasing threat of cyber attacks. Especially because the number of attacks has increased dramatically in recent years and that high tens of millions have already been paid in cyber extortion, it is clear that cybersecurity is no longer just “nice to have”, but essential for survival.
Jan-Oliver Wagner called for threats to be detected as early as possible and for risks to be managed proactively. He presented vulnerability management as “the first line of defense” against attackers. With Greenbone solutions, companies can continuously check their IT infrastructure for security vulnerabilities: “Vulnerability management is the basis of a sustainable and highly effective security strategy.” Security teams are often faced with the difficult task of assessing risks appropriately and making the right decisions. “The goal is to stay one step ahead of attackers. Our solutions not only identify security vulnerabilities, but also help prioritize which vulnerabilities need to be addressed most urgently.”
Inspiring Conversations and New Contacts: the Trade Fair Highlights
The trade fair enabled us to engage directly with industry visitors, customers and partners, answer their questions and better understand their perspectives. With many technical discussions in just three days, the number of visitors to our partner stand at ADN more than doubled compared to last year, reports Ingo Conrads, Chief Sales Officer: “We were particularly pleased about the many new prospects and partners with whom we were able to discuss many new business opportunities.”

Greenbone CEO Dr. Jan-Oliver Wagner giving the keynote “Be secure and stay secure” at it-sa 2024.
Many visitors already knew Greenbone as a brand, partly by OpenVAS in the past. But new products such as Greenbone Basic were also a discovery for many, showing how comprehensive and scalable our solutions have become – from entry-level to enterprise products for the public sector. The diversity of our portfolio and our services in particular generated surprise and interest. An overview of the various possible uses of our solutions is available on our website.
Thank You for the Successful Trade Fair!
it-sa 2024 was a great success and an inspiring experience for us. Once again, the trade fair showed how important vulnerability management has become and that Greenbone is making an important contribution to IT security. Many thanks to our distribution partner ADN for the excellent cooperation at the partner stand – and many thanks to all visitors for the interesting discussions and valuable feedback!
Together we are working to ensure that companies are secure – and stay secure.