The employees of Greenbone are currently developing a completely new scanner for version comparisons. The new vulnerability scanner “Notus” should significantly accelerate the comparison of software versions, CVEs and patches in the future.
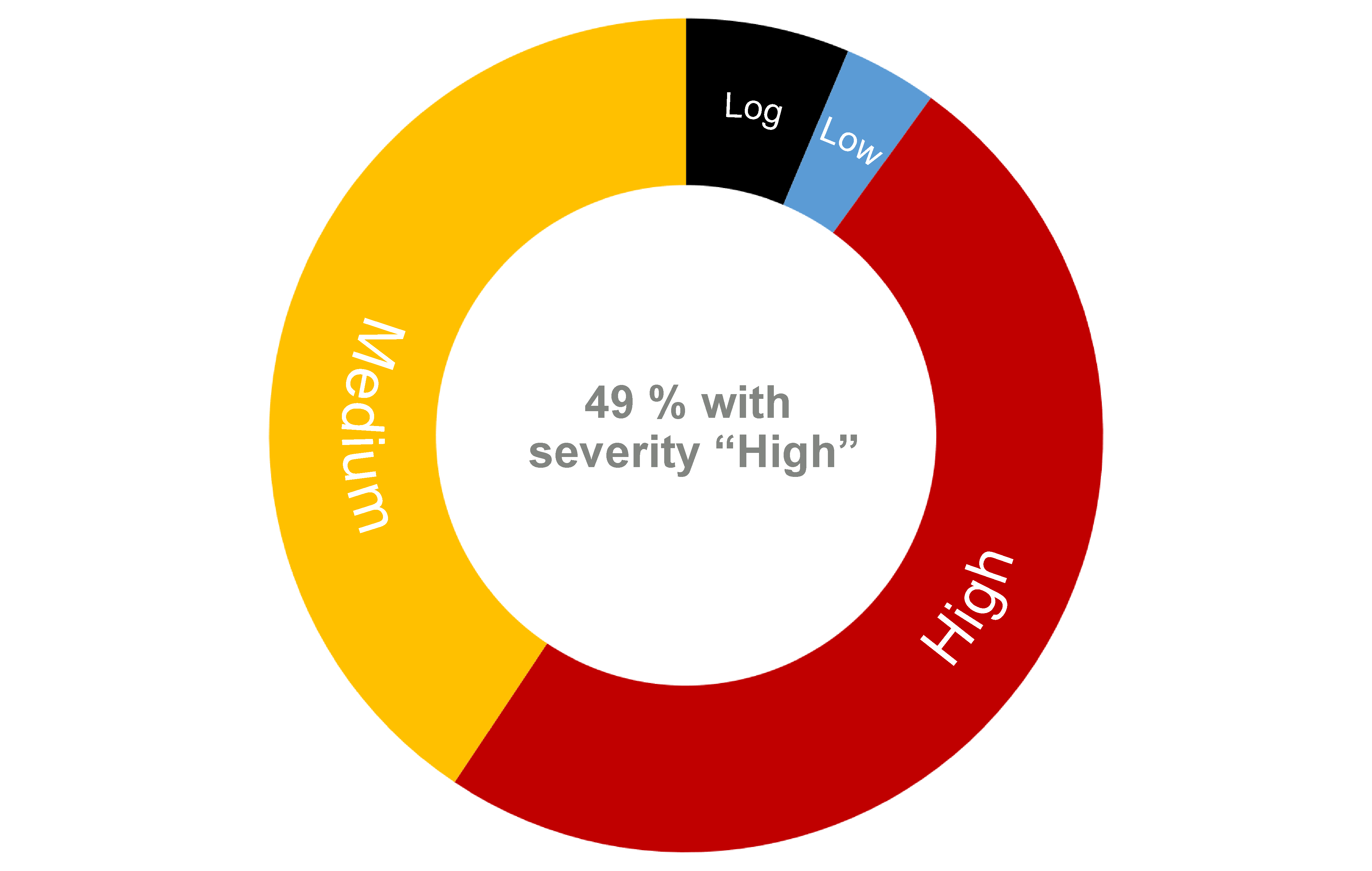
A large part of modern vulnerability management consists of comparing software versions. If you want to find out whether your server is immune to a vulnerability, you need to know which version of a particular software is running on that machine. For example, version 1 may be affected by a vulnerability that is already fixed in version 2. Whether vulnerability scanners like the new vulnerability scanner “Notus” issue a warning depends, among other things, heavily on the result of these comparisons.
Björn Ricks, Unit Lead Services & Platforms at Greenbone explains, “Such tasks alone accounted for more than a third of a scanner’s work, and the scanner we have optimized specifically for version comparisons is designed to speed this up significantly.”
Performance Shortcomings of Classic Scanners
At the beginning of the work of a classic scanner is an advisory with a gap found by experts. Greenbone employees then search for matching (affected) software versions and those that have already corrected the error. This information must now be made available to the scanner.
“It then rattles off the relevant servers and records software running there. For the actual scan, it essentially only gets the info about affected and fixed packages,” Ricks explains. “With the OpenVAS scanner and its predecessors, we usually had to start a separate process per version check, meaning a separate manually created script. Generating these scripts automatically is costly.”
JSON Data Helps Speed up the Scanner
The new scanner, on the other hand, only loads the data it needs from files in JSON format, an easy-to-read plain-text standard. “This means the logic for the tests is no longer in the scripts. This has many advantages: fewer processes, less overhead, less memory required.” Ricks believes the approach is “significantly more efficient.”
Elmar Geese, COO of Greenbone explains, “Our new Notus scanner will be a milestone for our users, it will significantly improve performance. Our well-known high detection quality as well as performance are key goals of our product strategy, and the new scanner supports this in an optimal way.”
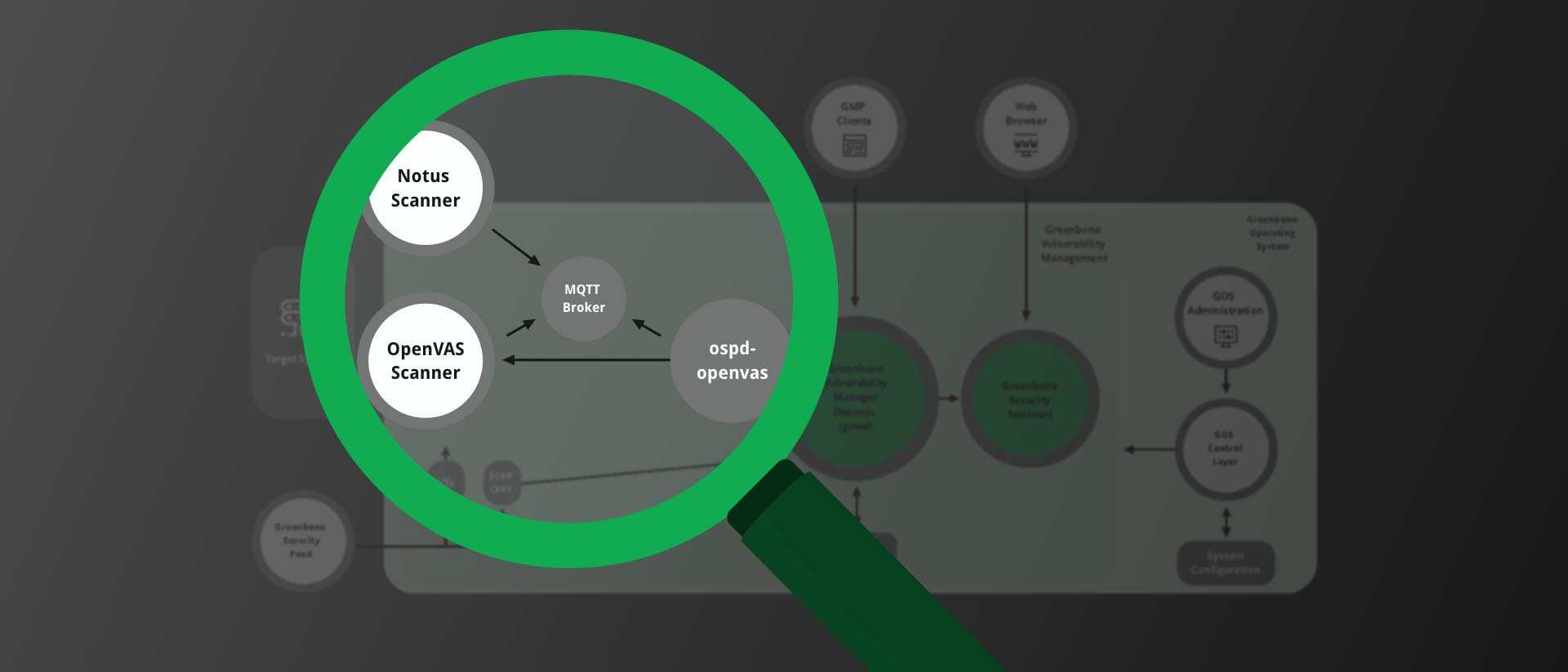
The “Notus” project consists of two parts: a “Notus” generator, which creates the JSON files containing information about vulnerable RPM/Debian packages, and the “Notus” scanner, which loads these JSON files and interprets the information from them. Greenbone plans to complete the new vulnerability scanner “Notus” in the next few months.
About Greenbone and OpenVAS
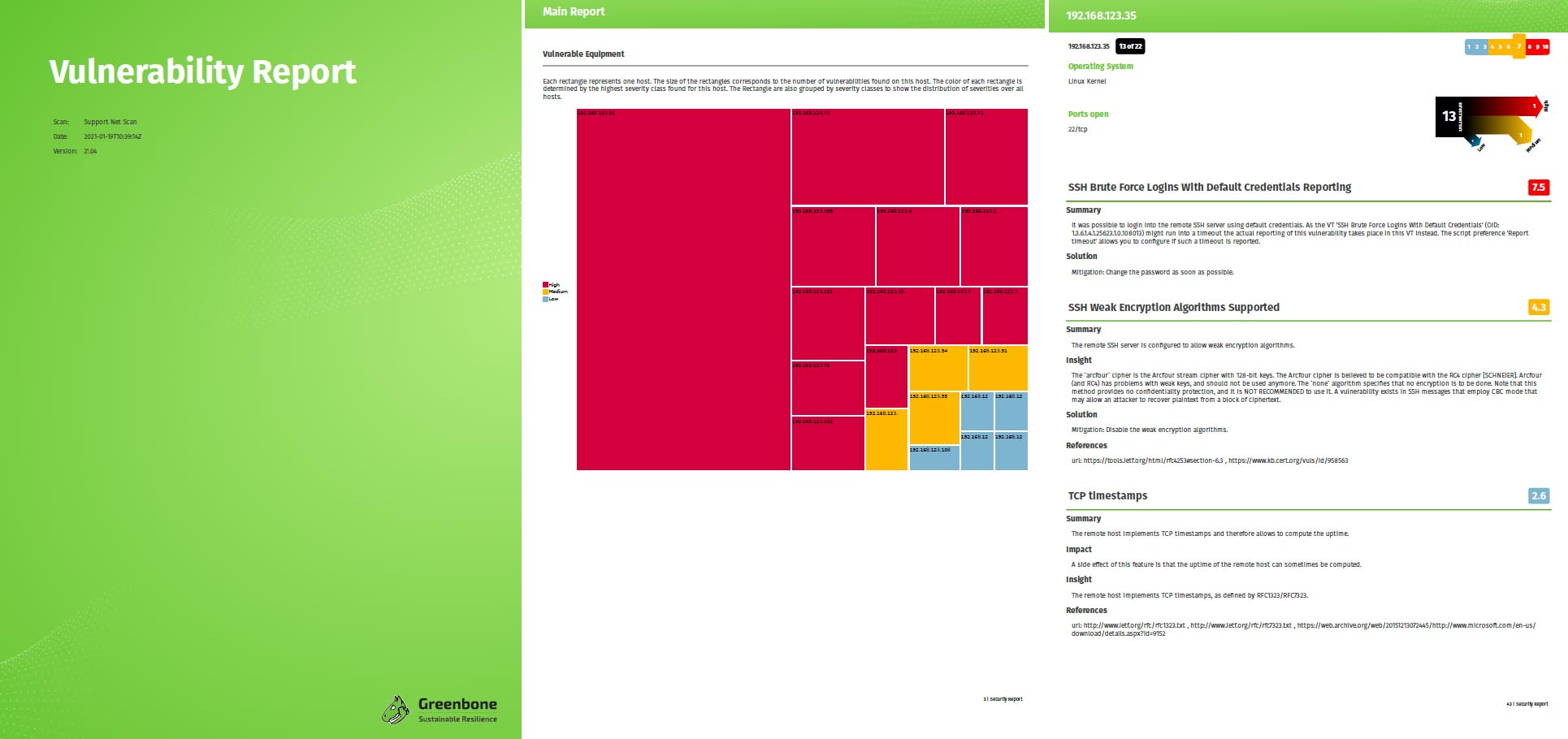
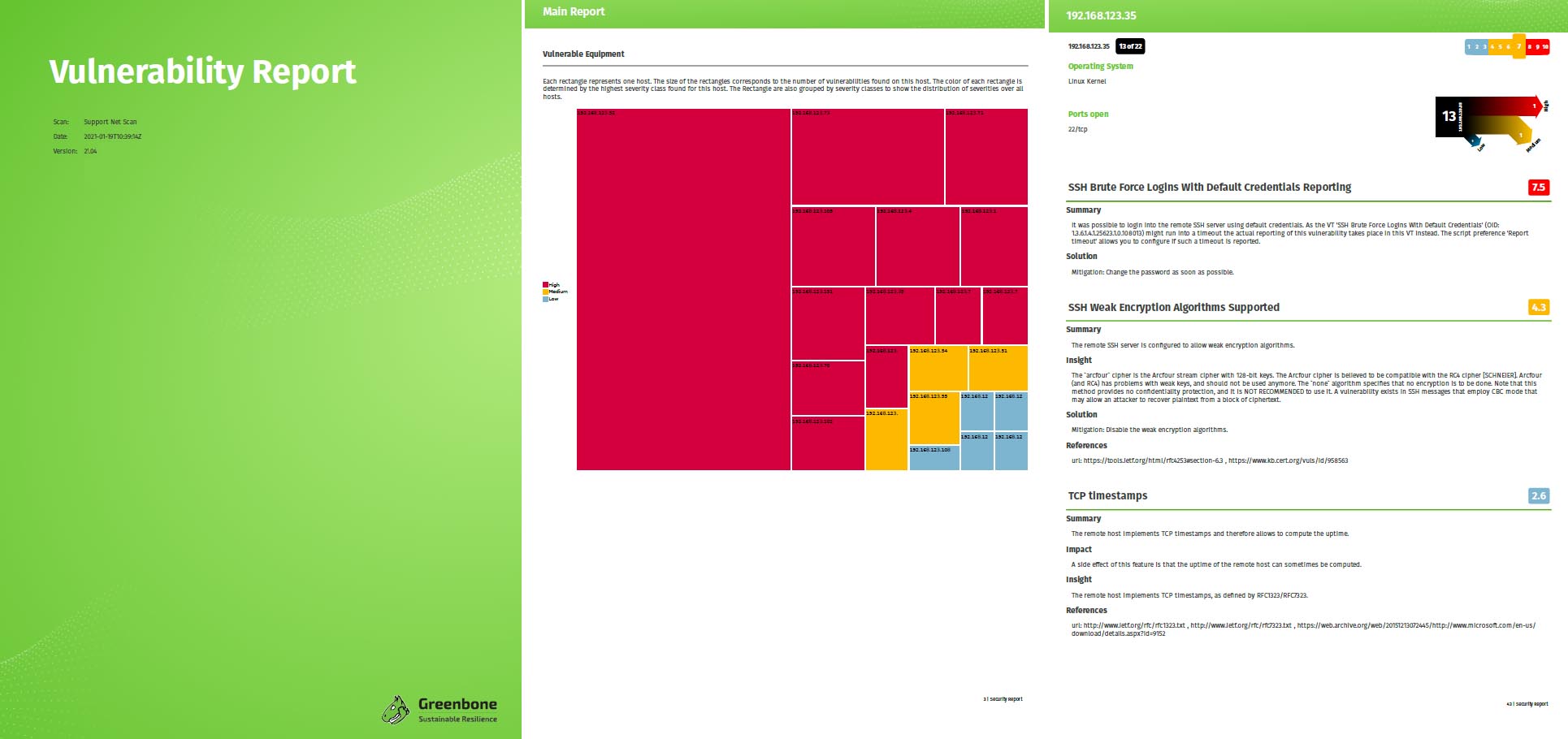
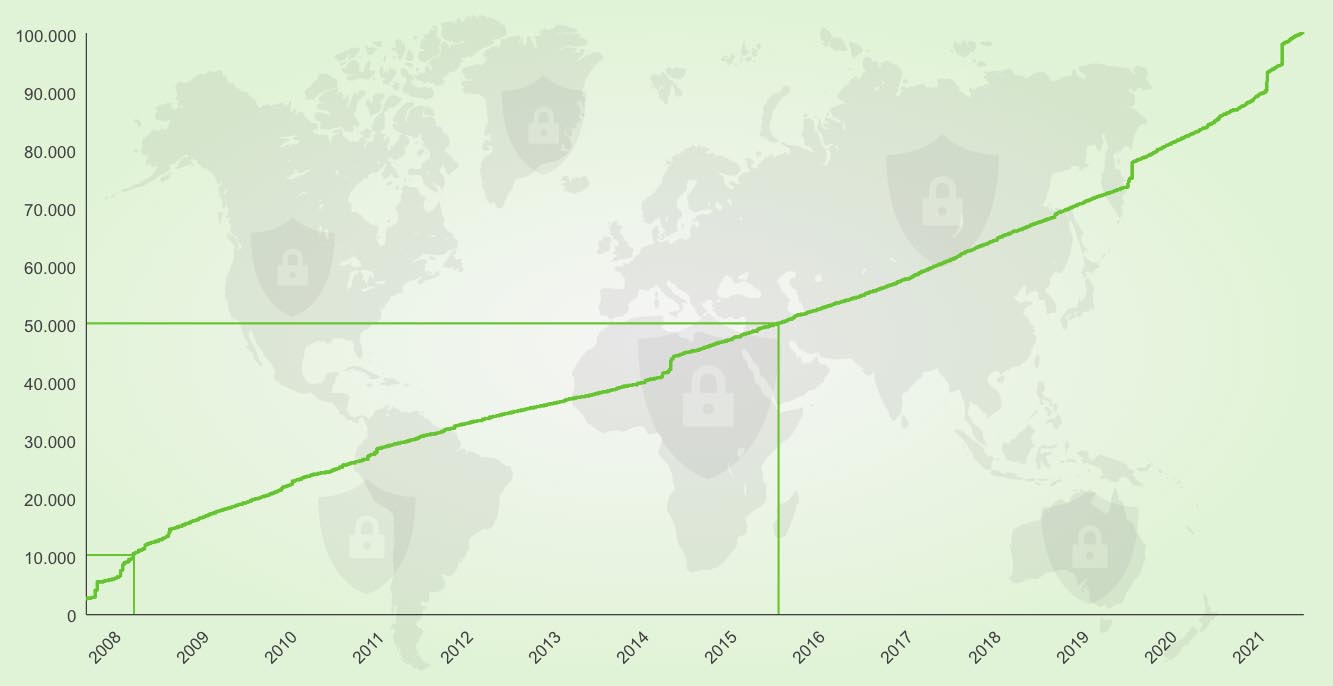
When the development team of the vulnerability scanner Nessus decided to stop working under open source licenses and switch to a proprietary business model in 2005, several forks of Nessus were created. Only one of them is still active: the Open Vulnerability Assessment System (OpenVAS).
The founding of Greenbone in 2008 aimed to drive the development of OpenVAS and provide users with professional vulnerability scanning support. Greenbone started to lead the further development of OpenVAS, added several software components and thus transformed OpenVAS into a comprehensive vulnerability management solution that still carries the values of free software. The first appliances hit the market in spring 2010.


 Since 2021-04-30, the latest GOS version – version 21.04 – is available and, as always, it brings a lot of new features and improvements! What exactly? Get an overview of all important changes with GOS 21.04 here!
Since 2021-04-30, the latest GOS version – version 21.04 – is available and, as always, it brings a lot of new features and improvements! What exactly? Get an overview of all important changes with GOS 21.04 here!